The Battle of Consolidation vs. Best-of-Breed, does more security mean better security?
You’re probably frequently scrutinizing whether or not your own organization’s cyber security is being properly managed. We’re constantly being bombarded with news of the latest cyber security attacks and hoping there are no gaps in our own organization’s security. With every new ransomware or phishing attack, the red flags start to wave. The immediate reaction is to ramp up our security and increase the number of vendors with the assumption that with these new products will keep us better protected. In reality, this unfortunately isn’t the case.
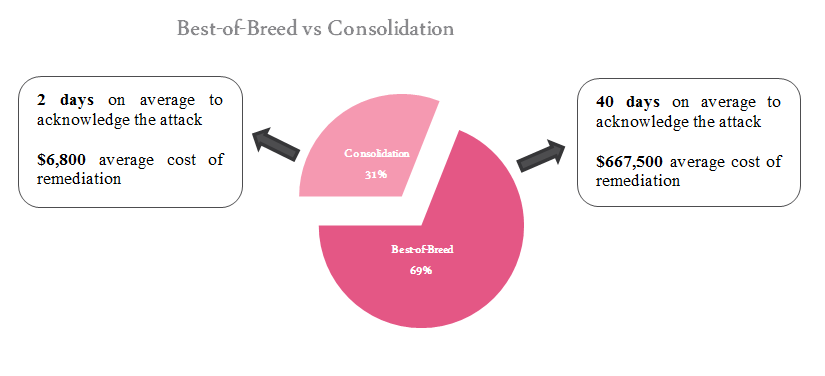
In a recent survey, executives were asked various questions about their cyber security requirements, including their day-to-day challenges and concerns. One of the questions asked was what do they consider the best approach. Overwhelmingly, C-level executives stated they were satisfied with a best-of-breed strategy and promoted it within their organization. However, once asked more probing questions regarding their security posture, it became obvious that their sense of what was best for their organization was a false sense of security, noting a significant difference in the attack recovery processes:
Organizations who chose a consolidation approach were capable of identifying and recovering from attacks 20 times faster on average, and at merely 1% of the cost than those choosing a best-of-breed strategy.
Reducing the number of vendors not only simplifies having to monitor multiple management consoles, between the various technologies but vendor consolidation allows for a higher level of security through superior integration versus decisions made across multiple vendor products. Additionally, it significantly reduces the time, cost and resources of the remediation process. Notably, Gartner has consistently cited in “ a single-vendor approach more effectively detects and stops advanced threats, increasing the efficiency of resources and reducing configuration and management problems while requiring less training and problem-solving costs.
Check Point CEO, Gil Shwed, highlighted on these issues during a recent event in Tel Aviv, Cyber Week 2017. Forbes published an article on Shwed’s lecture, “In cyberspace today our roof is very very leaky,” said Shwed. “With almost 1,600 cybersecurity companies worldwide, we hope that by building many point solutions we get protection from the rain. The reality is that the rain is coming through the inherent gaps in this architecture.” Shwed recommended replacing the widespread approach of using point solutions and mitigating the damage after the attack with a new approach of focusing on security prevention and using a unified architecture for managing security threats in the network, the cloud, and mobile devices.
An overgrowing concern within the cyber world is the scarcity of cyber professionals. Unfortunately, most companies suffer from this phenomenon and more will in upcoming years. This shortage directly translates into an inferior security posture and lack of knowledge needed to assess and adopt vendor products. There is an industry perception that by having multiple-vendors, you’re decreasing the risk of an attack, because “more will cover more”- therefore reducing costs and time. Our survey found this common misconception to be false.
A consolidated vendor approach through Check Point Infinity architecture drives simplicity and efficiency, and streamlines handling of events as they occur. Check Point Infinity architecture’s single management centrally correlates all types of events across all network environments, cloud services and mobile infrastructures. Check Point’s preemptive threat prevention strategy focuses on prevention rather than detection to block the most sophisticated attacks before they occur.
Our survey showed that the majority of organizations still prefer usage of various best-of-breed disparate security products. We can’t blame them for thinking this; we’re told as a society bigger is better. But the end results speak loud and clear: When it comes to security vendors, less is more.
The post Re-Thinking the Cyber Consolidation Paradigm appeared first on Check Point Blog.
from Check Point Blog http://ift.tt/2vb8hJ3