from Reuters: Technology News https://ift.tt/2r8mvYa
Facebook bids to keep data privacy case from EU's top court
from Reuters: Technology News https://ift.tt/2r8mvYa
Paper plane protesters urge Russia to unblock Telegram app
from Reuters: Technology News https://ift.tt/2I8Byui
U.S. tech fund Andra raises $500 million for new digital coin
from Reuters: Technology News https://ift.tt/2vXUzuF
Publishers rebuke Google's interpretation of EU privacy law
from Reuters: Technology News https://ift.tt/2raiHEF
Facebook seeks to block referral of privacy case to EU's top court
from Reuters: Technology News https://ift.tt/2FtviYP
U.S. top court turns away Google fight over business patents
from Reuters: Technology News https://ift.tt/2Kq4E74
U.S. Supreme Court to hear Google privacy settlement dispute
from Reuters: Technology News https://ift.tt/2vYEe96
Faulty Patch for Oracle WebLogic Flaw Opens Updated Servers to Hackers Again
from The Hacker News https://ift.tt/2Kpm6Z3
Broadcom says weak wireless chip demand to hurt revenue forecast
from Reuters: Technology News https://ift.tt/2KsabcW
UK lawmakers to quiz TSB over computer systems outage
from Reuters: Technology News https://ift.tt/2r7vZms
Asian telecom stocks face minimal 5G risks - JP Morgan
from Reuters: Technology News https://ift.tt/2jhwPsn
Cryptomining to The Dark Side
Key Findings:
- A once legitimate video download software site, OSDSoft, has moved into crypto-mining.
- Around 6000 machines have been infected in just a few months.
- Distributed by a fraudulent Adobe Flash Player update service, the malware is mining $700 of Monero crypto currency for the perpetrator each day.
Check Point researchers have recently discovered a site that although once (almost) legitimate has now moved closer to the Dark Side.
Back in 2011, OSDSoft was a site offering its audience free video download software to thousands of users around the world. Registered under the name of Ivan Koslov, it also had Facebook, Twitter and YouTube accounts marketing the website’s main and only product. It was to all intents and purposes a legitimate site.
In 2014 however, OSDSoft started to appear in more suspicious contexts as several Adwares and Potentially Unwanted Programs (PUPs) downloaded from it were spotted in the wild.
These adwares and PUPSs acted stealthily in order to evade regular anti-virus protections and performed environment checks to make sure they were not running on a virtual machine. It seems though that these PUPs and software bundles were only the beginning of this increasingly malicious campaign.
Ivan Darker
Towards the end of 2017, as the popularity of crypto currency miners grew, OSDSoft shifted some of its efforts toward mining the Monero crypto currency. As discussed on this blog previously, Monero cryptominers are becoming more popular due to the increased anonymity they provide and the profitability of mining Monero on regular PCs.
After some analysis, the Check Point Research team estimates that around 6000 machines have so far been infected and are earning the perpetrator behind OSDSoft approximately $700 per day from this mining operation alone. This stands out from other similar operations by infecting so many machines in a matter of months and spreading these PUPs for so many years.
How is OSDSoft’s Cryptominer Distributed?
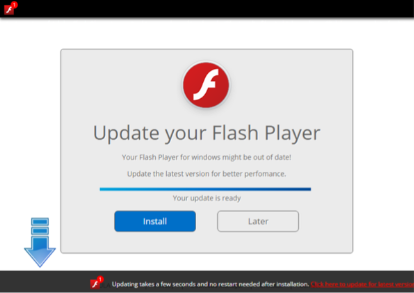
The miners are currently distributed by websites disguised as a legitimate Adobe Flash Player update service, telling the victim that their Flash version is outdated. Clicking anywhere on the screen would result in the malicious executable being downloaded. OSDSoft’s author does not want to waste any time in this campaign either, for while waiting for the Monerominer to download, the malignant websites additionally use the CoinHive cryptomining malware to mine through the browser and maximize his profits.
Fake Adobe Flash Player update service that distributes the cryptominer.
Furthermore, it is interesting to note that in this and other connected campaigns, it is legitimate hosting and file storage services such as AWS (Amazon Web Services), Dropbox and Github, that are being used to store and distribute the malicious cryptomining samples.
Victims are then directed to misleading malicious Flash Player domains such as flash2update[.]xyz, flashdownload[.]club, flashplayers[.]club and others via malvertising and referrals from shady websites.
Summary
Lately, security vendors are becoming more aware of the threat that PUP files pose and are increasingly treating them as malware. Dangers of a PUP can range from data theft and hijacking user traffic to possible remote code execution, as we have seen with our previous Fireball research.
OSDSoft, a website that started with seemingly innocent intentions serves as a case study in the need to be on constant alert. Although its author initially promoted video download software, the lure of high value crypto currencies lured him over to the dark side as the site became a PUP and cryptomining distribution platform.
For full technical details of this crypto-miner, please visit the Check Point Research blog.
The post Cryptomining to The Dark Side appeared first on Check Point Blog.
from Check Point Blog https://ift.tt/2jho1CV
Microsoft Windows NTFS Denial Of Service
from Check Point Update Services Advisories https://ift.tt/2vWE9mn
Google Chrome Promise Bug (CVE-2018-6106)
from Check Point Update Services Advisories https://ift.tt/2raPeLN
Microsoft Windows SNMP Denial of Service (CVE-2018-0967)
from Check Point Update Services Advisories https://ift.tt/2vWvIHG
T-Mobile, Sprint say $26 billion deal would give U.S. tech lead over China
from Reuters: Technology News https://ift.tt/2Kmnyvz
German regulator may require cable operators to open networks to third parties - FAZ
from Reuters: Technology News https://ift.tt/2r98EA1
Hackers Use LinkedIn Messages to Spread RAT Malware Through DLL Sideloading
Cybersecurity researchers have uncovered a new phishing campaign that exploits social media private messages to propagate malicious payloads...

-
Original release date: November 08, 2018 Summary JBoss Verify and EXploitation tool (JexBoss) is an open-source tool used by cybersecurity...
-
Original release date: May 21, 2018 The US-CERT Cyber Security Bulletin provides a summary of new vulnerabilities that have been recorded b...
-
Original release date: January 29, 2018 The US-CERT Cyber Security Bulletin provides a summary of new vulnerabilities that have been record...
-
It's no secret that learning how to code is one of the most important things you can do when it comes to the beginning or furthering pra...
-
Original release date: February 12, 2018 The US-CERT Cyber Security Bulletin provides a summary of new vulnerabilities that have been recor...
-
Original release date: February 26, 2018 The US-CERT Cyber Security Bulletin provides a summary of new vulnerabilities that have been recor...
-
Os estragos causados pelo ataque com ransomware ao Superior Tribunal de Justiça (STJ) ainda não são totalmente conhecidos. A Polícia Federa...
-
Original release date: March 9, 2020 The CISA Weekly Vulnerability Summary Bulletin is created using information from the NIST NVD . In som...
-
Original release date: October 26, 2020 The CISA Weekly Vulnerability Summary Bulletin is created using information from the NIST NVD . In...
-
Original release date: January 08, 2018 The US-CERT Cyber Security Bulletin provides a summary of new vulnerabilities that have been record...