This $350 "Anti-5G" Device Is Apparently Just a USB Stick
from Security Latest https://ift.tt/2TQlZwg
New Noise-Resilient Attack On Intel and AMD CPUs Makes Flush-based Attacks Effective
from The Hacker News https://ift.tt/36JtPg7
Exclusive – Any Mitron (Viral TikTok Clone) Profile Can Be Hacked in Seconds
from The Hacker News https://ift.tt/302lB1F
Google postpones Android 11 unveiling amid U.S. protests
from Reuters: Technology News https://ift.tt/2ArG70z
Exclusive: Zoom plans to roll out strong encryption for paying customers
from Reuters: Technology News https://ift.tt/36Gg1TO
Exclusive: Zoom plans to roll out strong encryption for paying customers only
from Reuters: Technology News https://ift.tt/3dgEfWZ
Brecha em software de código aberto expôs servidores da Cisco

A Cisco informou nesta quinta-feira (28) que seis servidores da empresa foram comprometidos devido a atividade de hackers.
Segundo a fabricante de produtos de telecomunicações, os agentes maliciosos afetaram sistemas do serviço de Virtual Internet Routing Lab Personal Edition (VIRL-PE), que permite a clientes criarem e testarem topologias de rede - isto é, a organização dos elementos de uma rede de comunicação - sem a necessidade de instalar equipamentos.
Os hackers exploraram falhas críticas no serviço de software de código aberto Salt que estruturava os servidores da Cisco. O Salt é muito usado para serviços de automação, bem como na implantação de gerenciamento de sistemas de data centers.
Brechas de segurança
As vulnerabilidades do software vieram a público no fim de abril, porém, a Cisco detectou as brechas de segurança em suas redes somente no dia 7 de maio. A empresa então desativou os servidores, e promoveu ajustes para remediar o problema.
A companhia lançou duas atualizações para os serviços de VIRL-PE e para o produto relacionado Cisco Modeling Labs Corporate Edition. A corporação aponta que, sem as atualizações, qualquer versão de ambos serviços pode permanecer vulnerável.
As vulnerabilidades correspondem a um desvio de autenticação, identificado como CVE-2020-11651, e uma passagem de diretório, CVE-2020-11652. Juntos, elas permitem o acesso não autorizado a todo o sistema de arquivos dos servidores configurados em Salt.

Em fevereiro, uma outra vulnerabilidade identificada em aparelhos da Cisco chamada CDPwn permitia que malfeitores capturassem o aúdio e o vídeo de equipamentos da companhia. Imagem: Armis
Prevenção
A Cisco não foi a única empresa a sofrer ataques cibernéticos devido a problemas no patch do Salt, como pontua o site Ars Technica. No início de maio, a plataforma de blogs Ghost informou que hackers invadiram seus servidores e infectaram os sistemas com malwares de mineração de bitcoins. A empresa de soluções digitais Xen-Orchestra também sofreu do mesmo problema.
Diante do retrospecto de ataques é fundamental que qualquer empresa ou pessoa que utilize serviços que dependam do Salt garanta que eles estejam sempre atualizados.
Fonte: Ars Technica
from Olhar Digital :: Segurança https://ift.tt/3cjcR9E
Italian magistrates target Uber Italia over alleged rider exploitation: sources
from Reuters: Technology News https://ift.tt/2AqhSzR
China's Kunlun says U.S approves sale of Grindr to investor group
from Reuters: Technology News https://ift.tt/36GG79a
Servidor de e-mails Exim é explorado por hackers desde agosto de 2019

A Agência de Segurança Nacional americana (NSA) divulgou que o grupo de hackers militares russos conhecido como Sandworm Team tem explorado uma aplicação servidora de e-mails desde agosto de 2019. O mesmo grupo interferiu nas eleições presidenciais dos EUA em 2016, desencadeando um ataque de malware devastador no ano seguinte.
O comunicado da agência publicado na quinta-feira (28) foi incomum, visto que a vulnerabilidade crítica no Exim Mail Transfer Agent - geralmente executado em sistemas operacionais do tipo Unix - foi identificada há quase um ano, quando um patch foi lançado. Na época, foi pedido aos usuários atualizarem o Exim para a versão mais recente.

Falha atinge o servidor de e-mails Exim/Foto: Reprodução
A falha que está sendo explorada, CVE-2019-10149, permite que um invasor remoto execute comandos e códigos de sua escolha. Os hackers se aproveitaram do deslize e acessaram a aplicação usando um e-mail criado especificamente para tal. Eles conseguiram instalar programas, desativar configurações de segurança e executar scripts adicionais para explorar a rede.
A NSA não disse, no entanto, qual foi o alvo do ataque dos hackers militares russos. Uma pista teria sido dada por altos funcionários da Agência de Inteligência americana (CIA), que alertaram nos últimos meses sobre agentes do complexo russo Kremlin envolvidos em atividades que podem ameaçar a integridade das eleições presidenciais de novembro.
Via: APNews
from Olhar Digital :: Segurança https://ift.tt/3gyHJX2
Trump threatens 'shooting' response to Minneapolis riot over police killing
from Reuters: Technology News https://ift.tt/3daL50i
COVID-19 robot patrol rolled out in Belgian hospitals
from Reuters: Technology News https://ift.tt/36JpVnq
VMware Releases Security Updates for Multiple Products
VMware has released security updates to address vulnerabilities affecting multiple products. An attacker could exploit one of these vulnerabilities to take control of an affected system.
The Cybersecurity and Infrastructure Security Agency (CISA) encourages users and administrators to review the VMware Security Advisory VMSA-2020-0011 and apply the necessary updates.
This product is provided subject to this Notification and this Privacy & Use policy.
from CISA All NCAS Products https://ift.tt/3gBBxxq
Cisco Releases Security Updates for CML and VIRL-PE
Cisco has released security updates to address SaltStack FrameWork vulnerabilities in Cisco Modeling Labs Corporate Edition (CML) and Virtual Internet Routing Lab Personal Edition (VIRL-PE). A remote attacker could exploit these vulnerabilities to take control of an affected system.
The Cybersecurity and Infrastructure Security Agency (CISA) encourages users and administrators to review the Cisco Security Advisory and apply the necessary updates or workaround.
This product is provided subject to this Notification and this Privacy & Use policy.
from CISA All NCAS Products https://ift.tt/3dgEIbM
Nova vulnerabilidade crítica no Android pode afetar milhões de aparelhos

A empresa de pesquisa de segurança norueguesa Promon descobriu uma nova vulnerabilidade crítica que pode afetar uma grande quantidade de smartphones Android. A falha permite que hackers mascarem aplicativos maliciosos como qualquer outro e, dessa forma, rastreiem o usuário tendo acesso a informações pessoais.
Chamada StrandHogg 2.0 e com o número CVE-2020-0096, a vulnerabilidade está presente em todos os celulares com Android, com exceção daqueles que possuem a versão mais recente do sistema operacional, o Android 10. Isso quer dizer que milhões de dispositivos podem ser afetados, já que o Google afirmou que apenas 16% dos 2,5 bilhões de dispositivos tiveram a última versão instalada.
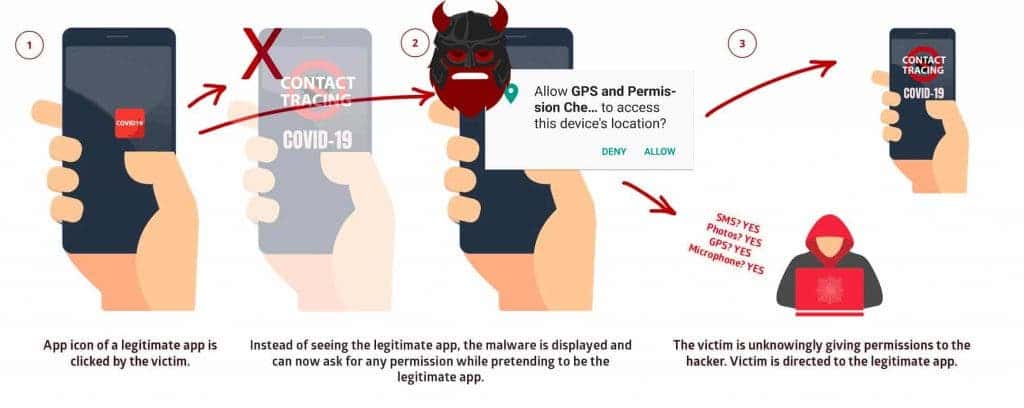
A mesma empresa norueguesa descobriu a StrandHogg original no fim de 2019. Segundo os especialistas, a falha era usada para roubar informações bancárias, senhas, logins e monitorar a atividade do usuário. Segundo a Promon, o StrandHogg 2.0 permite ataques ainda mais complexos.
Via: GizChina
from Olhar Digital :: Segurança https://ift.tt/2ZOb9KJ
This Week in Security News: How the Cybercriminal Underground Has Changed in 5 Years and the NSA Warns of New Sandworm Attacks on Email Servers

Welcome to our weekly roundup, where we share what you need to know about the cybersecurity news and events that happened over the past few days. This week, learn about how, over the past five years, the cybercriminal underground has seen a major shift to new platforms, communications channels, products, and services. Also, read about a new wave of Sandworm cyberattacks against email servers conducted by one of Russia’s most advanced cyber-espionage units.
Read on:
How the Cybercriminal Underground Has Changed in 5 Years
Trend Micro has been profiling the underground cybercrime community for many years. Over the past five years, it has seen a major shift to new platforms, communications channels, products, and services, as trust on the dark web erodes and new market demands emerge. Trend Micro expects the current pandemic to create yet another evolution, as cyber-criminals look to take advantage of new ways of working and systemic vulnerabilities.
Shadowserver, an Internet Guardian, Finds a Lifeline
In March, internet security group Shadowserver learned that longtime corporate sponsor Cisco was ending its support. With just weeks to raise hundreds of thousands of dollars to move its data center out of Cisco’s facility—not to mention an additional $1.7 million to make it through the year—the organization was at real risk of extinction. Ten weeks later, Shadowserver has come a long way toward securing its financial future. This week, Trend Micro committed $600,000 to Shadowserver over three years, providing an important backbone to the organization’s fundraising efforts.
#LetsTalkSecurity: No Trust for the Wicked
This Week, Rik Ferguson, vice president of Security Research at Trend Micro, hosted the fourth episode of #LetsTalkSecurity featuring guest Dave Lewis, Global Advisory CISO at Duo Security. Check out this week’s episode and follow the link to find information about upcoming episodes and guests.
Principles of a Cloud Migration – Security W5H – The HOW
Security needs to be treated much like DevOps in evolving organizations, meaning everyone in the company has a shared responsibility to make sure it is implemented. It is not just a part of operations, but a cultural shift in doing things right the first time – security by default. In this blog from Trend Micro, learn 3 tips to get you started on your journey to securing the cloud.
What’s Trending on the Underground Market?
Trust has eroded among criminal interactions in the underground markets, causing a switch to e-commerce platforms and communication using Discord, which both increase user anonymization, a new Trend Micro report reveals. Determined efforts by law enforcement appear to be having an impact on the cybercrime underground as several forums have been taken down by global police entities.
Is Cloud Computing Any Safer from Malicious Hackers?
Cloud computing has revolutionized the IT world, making it easier for companies to deploy infrastructure and applications and deliver their services to the public. The idea of not spending millions of dollars on equipment and facilities to host an on-premises data center is a very attractive prospect to many. But is cloud computing any safer from malicious threat actors? Read this blog from Trend Micro to find out.
Smart Yet Flawed: IoT Device Vulnerabilities Explained
The variety and range of functions of smart devices present countless ways of improving different industries and environments. While the “things” in the internet of things (IoT) benefits homes, factories, and cities, these devices can also introduce blind spots and security risks in the form of vulnerabilities. Vulnerable smart devices open networks to attack vectors and can weaken the overall security of the internet. For now, it is better to be cautious and understand that “smart” can also mean vulnerable to threats.
Cyberattacks Against Hospitals Must Stop, Says Red Cross
Immediate action needs to be taken to stop cyberattacks targeting hospitals and healthcare organizations during the ongoing coronavirus pandemic – and governments around the world need to work together to make it happen, says a newly published open letter signed by the International Committee of the Red Cross, former world leaders, cybersecurity executives and others.
Securing the 4 Cs of Cloud-Native Systems: Cloud, Cluster, Container, and Code
Cloud-native technologies enable businesses to make the most of their cloud resources with less overhead, faster response times, and easier management. Like any technology that uses various interconnected tools and platforms, security plays a vital role in cloud-native computing. Cloud-native security adopts the defense-in-depth approach and divides the security strategies utilized in cloud-native systems into four different layers.
Coinminers Exploit SaltStack Vulnerabilities CVE-2020-11651 and CVE-2020-11652
Researchers from F-Secure recently disclosed two high-severity vulnerabilities in SaltStack Salt: CVE-2020-11651, an authentication bypass vulnerability, and CVE-2020-11652, a directory traversal vulnerability. These can be exploited by remote, unauthenticated attackers, and all versions of SaltStack Salt before 2019.2.4 and 3000 before 3000.2 are affected. Trend Micro has witnessed attacks exploiting these vulnerabilities, notably those using cryptocurrency miners.
PonyFinal Ransomware Targets Enterprise Servers Then Bides Its Time
A Java-based ransomware known as PonyFinal has emerged, targeting enterprise systems management servers as an initial infection vector. It exfiltrates information about infected environments, spreads laterally and then waits before striking — the operators go on to encrypt files at a later date and time, when the likelihood of the target paying is deemed to be the most likely.
Qakbot Resurges, Spreads through VBS Files
Trend Micro has seen events that point to the resurgence of Qakbot, a multi-component, information-stealing threat first discovered in 2007. Feedback from Trend Micro’s sensors indicates that Qakbot detections increased overall. A notable rise in detections of a particular Qakbot sample (detected by Trend Micro as Backdoor.Win32.QBOT.SMTH) was also witnessed in early April.
CSO Insights: SBV’s Ian Keller on the Challenges and Opportunities of Working Remotely
The COVID-19 pandemic has forced businesses to change the way they operate. These abrupt changes come with a unique set of challenges, including security challenges. Ian Keller, Chief Security Officer of SBV Services in South Africa, sat down with Trend Micro and shared his thoughts on how SBV is coping with the current pandemic, the main challenges they faced when transitioning their staff to remote work, as well as how they plan to move forward.
NSA Warns of New Sandworm Attacks on Email Servers
The US National Security Agency (NSA) has published a security alert warning of a new wave of cyberattacks against email servers, attacks conducted by one of Russia’s most advanced cyber-espionage units. The NSA says that members of Unit 74455 of the GRU Main Center for Special Technologies (GTsST), a division of the Russian military intelligence service, have been attacking email servers running the Exim mail transfer agent (MTA).
In the second part of this five series column, Trend Micro looks at the security risks to be aware of when promoting smart factories by examining overlooked attack vectors, feasible attack scenarios, and recommended defense strategies. This column is especially applicable for architects, engineers, and developers who are involved in smart factory technology.
Factory Security Problems from an IT Perspective (Part 2): People, Processes, and Technology
This blog is the second in a series that discusses the challenges that IT departments face when they are assigned the task of overseeing cybersecurity in factories and implementing measures to overcome these challenges. In this article, Trend Micro carries out an analysis to uncover the challenges that lie in the way of promoting factory security from an IT perspective.
21 Tips to Stay Secure, Private, and Productive as You Work from Home on Your Mac
If you brought a Mac home from the office, it’s likely already set up to meet your company’s security policies. But what if you are using your personal Mac to work from home? You need to outfit it for business, to protect it and your company from infections and snooping, while ensuring it continues to run smoothly over time. In this blog, learn 21 tips for staying secure, private, and productive while working from home on your Mac.
Surprised by the new wave of Sandworm attacks? Share your thoughts in the comments below or follow me on Twitter to continue the conversation: @JonLClay.
The post This Week in Security News: How the Cybercriminal Underground Has Changed in 5 Years and the NSA Warns of New Sandworm Attacks on Email Servers appeared first on .
from Trend Micro Simply Security https://ift.tt/2Mn0L53
German regulator examines stock trades by Wirecard CEO
from Reuters: Technology News https://ift.tt/3et666E
Indian IT firm Wipro names Capgemini's Thierry Delaporte as CEO
from Reuters: Technology News https://ift.tt/36EdPw7
Uber launches hourly ride booking option in some U.S. cities
from Reuters: Technology News https://ift.tt/2ZKGZZ3
Least Privilege for AWS Lambda Security
By, Hillel Sollow, Serverless Security R&D If you are a security professional or at least someone who cares enough about security you will appreciate the importance of restricting privilege access to resource as a means to maximize security. More so, if you are familiar with AWS serverless technology, you should also be familiar with the…
The post Least Privilege for AWS Lambda Security appeared first on Check Point Software.
from Check Point Software https://ift.tt/2TSfybR
Hackers Use LinkedIn Messages to Spread RAT Malware Through DLL Sideloading
Cybersecurity researchers have uncovered a new phishing campaign that exploits social media private messages to propagate malicious payloads...

-
Original release date: November 08, 2018 Summary JBoss Verify and EXploitation tool (JexBoss) is an open-source tool used by cybersecurity...
-
Original release date: May 21, 2018 The US-CERT Cyber Security Bulletin provides a summary of new vulnerabilities that have been recorded b...
-
Original release date: January 29, 2018 The US-CERT Cyber Security Bulletin provides a summary of new vulnerabilities that have been record...
-
It's no secret that learning how to code is one of the most important things you can do when it comes to the beginning or furthering pra...
-
Original release date: February 12, 2018 The US-CERT Cyber Security Bulletin provides a summary of new vulnerabilities that have been recor...
-
Original release date: February 26, 2018 The US-CERT Cyber Security Bulletin provides a summary of new vulnerabilities that have been recor...
-
Os estragos causados pelo ataque com ransomware ao Superior Tribunal de Justiça (STJ) ainda não são totalmente conhecidos. A Polícia Federa...
-
Original release date: March 9, 2020 The CISA Weekly Vulnerability Summary Bulletin is created using information from the NIST NVD . In som...
-
Original release date: October 26, 2020 The CISA Weekly Vulnerability Summary Bulletin is created using information from the NIST NVD . In...
-
Original release date: January 08, 2018 The US-CERT Cyber Security Bulletin provides a summary of new vulnerabilities that have been record...