By Richard Clayton, Check Point Research Marketing
Mark Twain once wrote there are few things harder to put up with than the annoyance of a good example. He would have had a hard time then putting up with the latest shining example of why it is so necessary to have an advanced security solution installed on your mobile device.
In a latest discovery, Check Point Research has come across a massive mobile adware campaign that has already delivered an eye-watering 147 million downloads across almost 210 infected apps on the Google Play Store. Dubbed ‘SimBad’, due to most of the infected apps being simulator games, the worldwide campaign makes use of the phone unbearable by displaying countless ads outside of the application, with no visible way to uninstall the incriminating apps.
The Height of Annoyance
The infected apps all use a malicious SDK to carry out their operation. While there are other SDKs available for the monetization of mobile apps, the game developers have chosen to use an SDK they benefits them by displaying a far higher number of ads in order to increase their profits.
The apps’ malicious behavior includes:
- Showing ads outside of the application, for example when the user unlocks their phone or uses other apps.
- Constantly opening Google Play or 9Apps Store and redirecting to another particular application, so the developer can profit from additional installations.
- Hiding its icon from the launcher in order to prevent uninstallation.
- Opening a web browser with links provided by the app developer.
- Downloading APK files and asking the user to install it.
- Searching a word provided by the app in Google Play.
This is not the first time a third party element has been used to infect the supply chain however.
Beware of the Supply Chain Attack
Modern software applications, such as websites or mobile phone apps, are built using complex supply chains of third party libraries or open source components. After all, why reinvent the wheel when there are off-the-shelf solutions that can help an organization’s software engineers to build applications that help enable business operations? There is, however, a downside to using third-party code – Supply Chain Attacks.
In supply chain attacks, attackers leverage trusted third party vendors to deliver malware to unsuspecting customers by inserting malware into third-party code. From the attacker’s point of view, poisoning a company’s software supply chain by infecting one of the components within it is highly tempting and arguably easier than a direct attack on the organization itself.
While there have been notable examples of such attacks, including the massively disruptive NotPetya attack and the compromise of the widely used CCleaner security tool in 2017, in another alarming discovery by Check Point researchers, another group of Android applications were found to be mass harvesting contact information from users’ mobile phones without their knowledge or consent via malware hidden inside a monetization Software Development Kit (SDK).
Infecting the Supply Chain
Check Point Research recently discovered a group of Android applications to have malware hidden inside a monetization Software Development Kit (SDK), named SWAnalytics, which was integrated into seemingly innocent Android applications published in major third party Chinese app stores. After app installation, whenever SWAnalytics senses victims opening an infected application, or rebooting their phones, it silently steals and sends their entire list of contacts to a remote server.
Until now, 12 infected applications, the majority of which being system utility apps, have been downloaded a staggering total of over 111 million times. In theory, this means the attacker could have collected the names and contact numbers of a third of China’s entire population.
Such data could, of course, circulate in underground markets for further exploit, ranging from rogue marketing, targeted telephone scam or friend referral program abuse.
Interestingly, in July 2018 US intelligence agencies issued a report highlighting concerns that software supply chain attacks represent an emerging threat from China that could erode America’s long-term competitive economic advantage.
Why Supply Chain Attacks Are Easy Pickings for Attackers
Because organizations have often invested more heavily in technology to protect their data and networks, cyber criminals must find innovative ways to circumvent those defenses — including exploiting vulnerabilities in the software supply chain. Through the supply chain threat actors can reach a wide range of organizations due to third party code that is used by so many software engineers across all industries. But the reasons go deeper than this.
For one, organizations trust that the third party code they use has built-in security. Unfortunately this is not always the case. As third-party providers often prioritize speed to market over security, it means their code can easily be intercepted and compromised. By the time it is used by the software engineer within an organization, it could well be too late and risks the final software application itself being compromised too.
Attackers are well aware that DevOps teams are driven by speed to make organizations more agile so often develop and deploy applications without the necessary security checks. Knowing this allows them to take advantage of these sacrifices of security concerns.
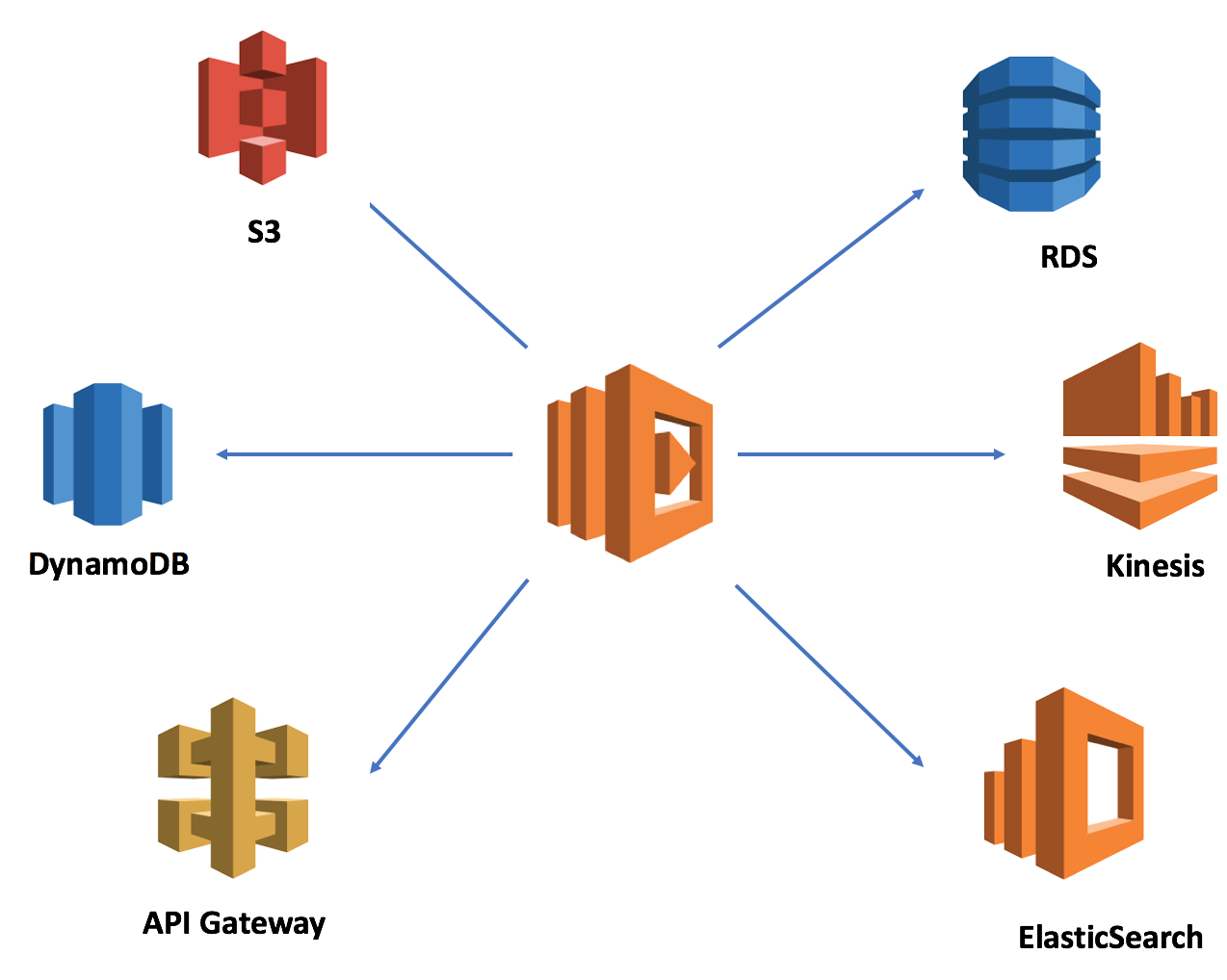
Furthermore, there is no good way to partition third party libraries or code from your organization’s in-house built code. As a result, it all runs within the same privilege. That means that anything the application can do, all the libraries can also do. So if the application can access your database, there is nothing to stop your libraries from doing the same.
Protecting Against Supply Chain Attacks
So is there is anything that can be done to prevent supply chain attacks affecting your organization?
Unfortunately, there is no easy answer for defending against these types of attacks. Organizations need to understand what commercial and open source products they are using, and be aware of and prepared for potential attacks using legitimate software as a vector.
Adopting a “hygiene first” approach to your organization’s security architecture will give you full visibility into your IT environment and help address any blind spots. As more and more applications are added to your IT ecosystem security teams often struggle to keep updated on who is installing such applications and where. As a result, these applications can quickly become a liability.
As a result, it is important to have cutting-edge end-point prevention solutions, networking controls/segmentation, and improved controls around privileged credentials to prevent an attack from spreading across your entire corporate network.
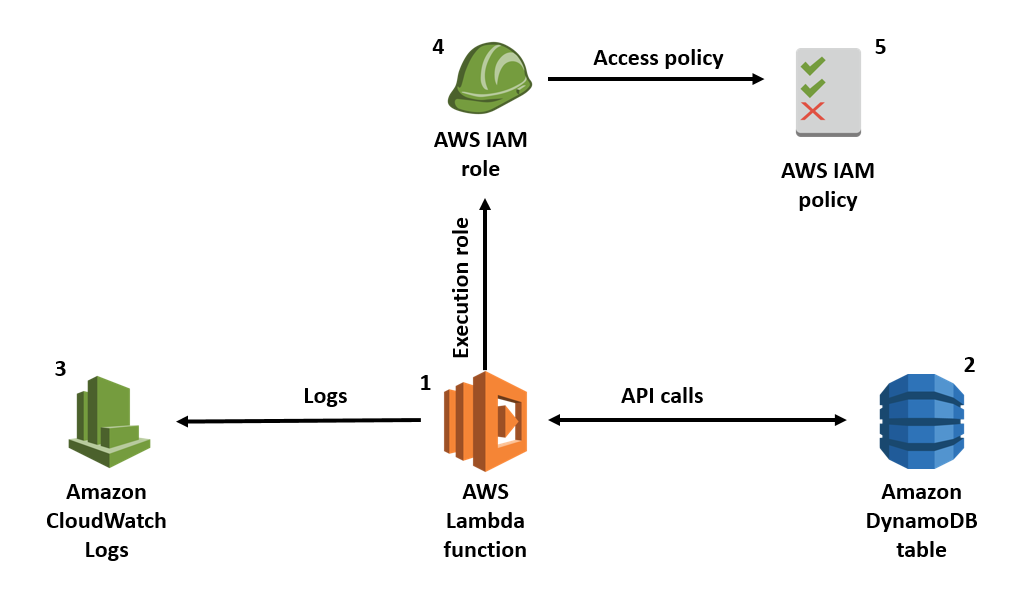
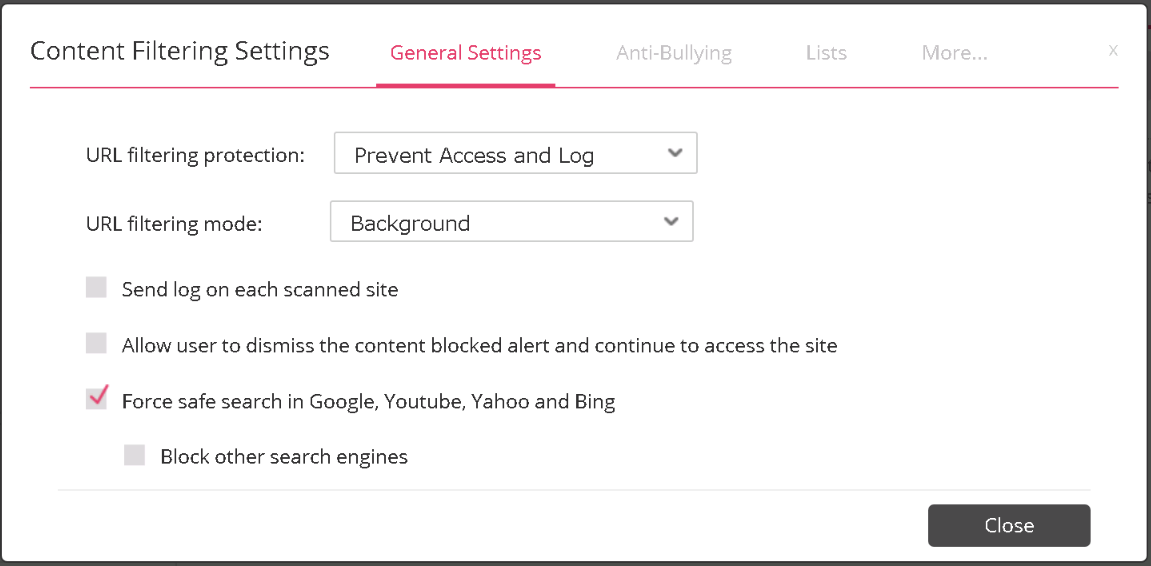
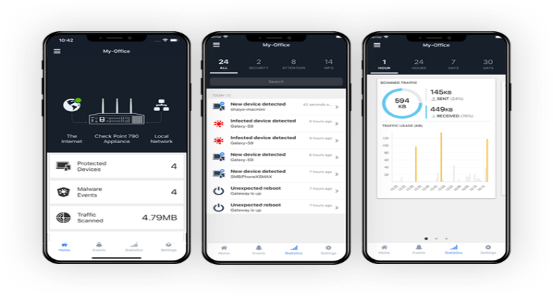
SandBlast Mobile’s unique security infrastructure, On-device Network Protection, delivers threat prevention capabilities to enterprise mobile devices that were previously only available in network and endpoint security solutions. By inspecting and controlling all network traffic on the device, SandBlast Mobile prevents phishing attacks across all apps, email, SMS, iMessage and messaging apps. In addition, the solution prevents accessing malicious or restricted websites, and infected devices from accessing corporate resources and communicating with botnets. To ensure data and user privacy, SandBlast Mobile validates cellular traffic on the device itself without routing data through a corporate gateway.
Conclusion
While the software supply chain is crucial for DevOps teams to build and deploy business applications quickly and efficiently, the risks they pose can easily undermine and compromise your organization’s security.
The proliferation of third-party software used within organizations, though, is not likely to slow down. Along with this growth, supply chain attacks are also likely to increase due to insufficient protection of software development and distribution channels.
As a result, within this complex threat landscape the best protection against destructive software supply chain attacks is to leverage advanced threat prevention technologies, powered by advanced threat intelligence, combined with a ‘hygiene first’ approach to protecting your organization’s digital assets.
Check Point’s SandBlast Mobile protects against info stealing malware such as that seen in the above research. For more details, please visit Sand Blast Mobile.
For full technical details about the Chinese SDK apps, please visit Check Point Research.
For full technical details about the SimBad malicious apps, please visit Check Point Research.
The post Mobile Supply Chain Attacks Are More Than Just an Annoyance appeared first on Check Point Software Blog.
from Check Point Software Blog https://ift.tt/2TzlNDm


 Jsecoin – JavaScript miner that can be embedded in websites. With JSEcoin, you can run the miner directly in your browser in exchange for an ad-free experience, in-game currency and other incentives.
Jsecoin – JavaScript miner that can be embedded in websites. With JSEcoin, you can run the miner directly in your browser in exchange for an ad-free experience, in-game currency and other incentives.